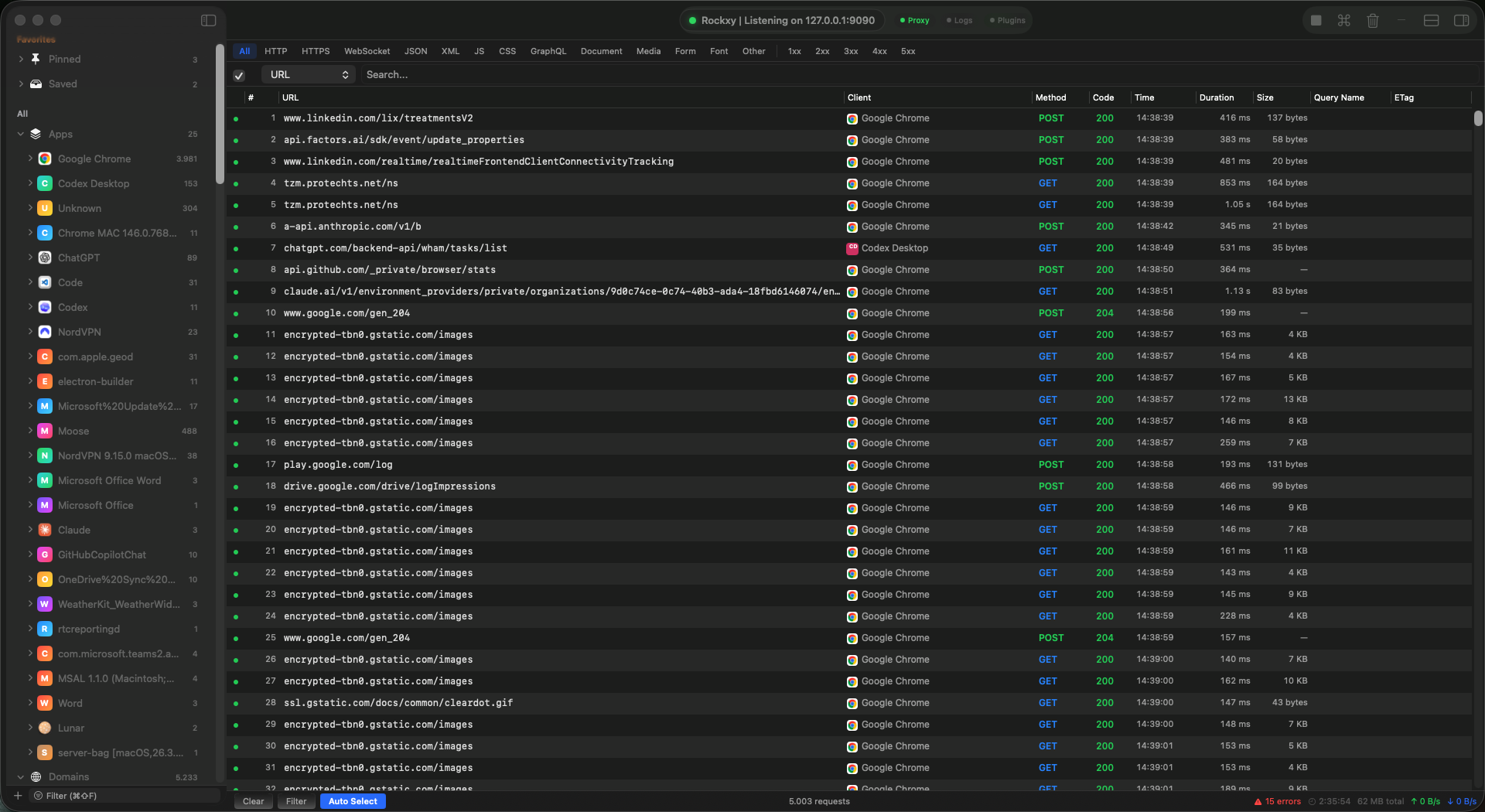
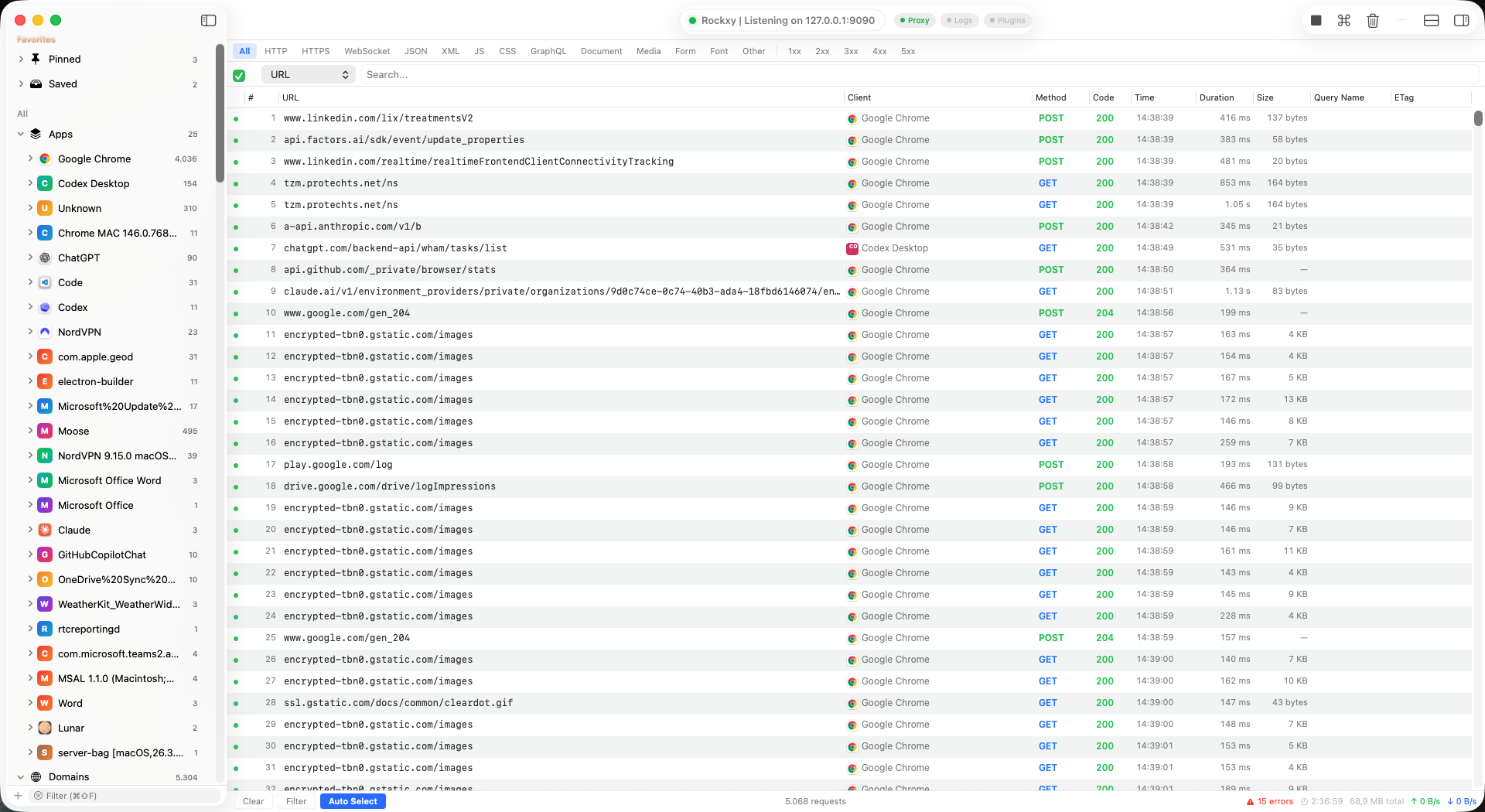
What Rockxy does
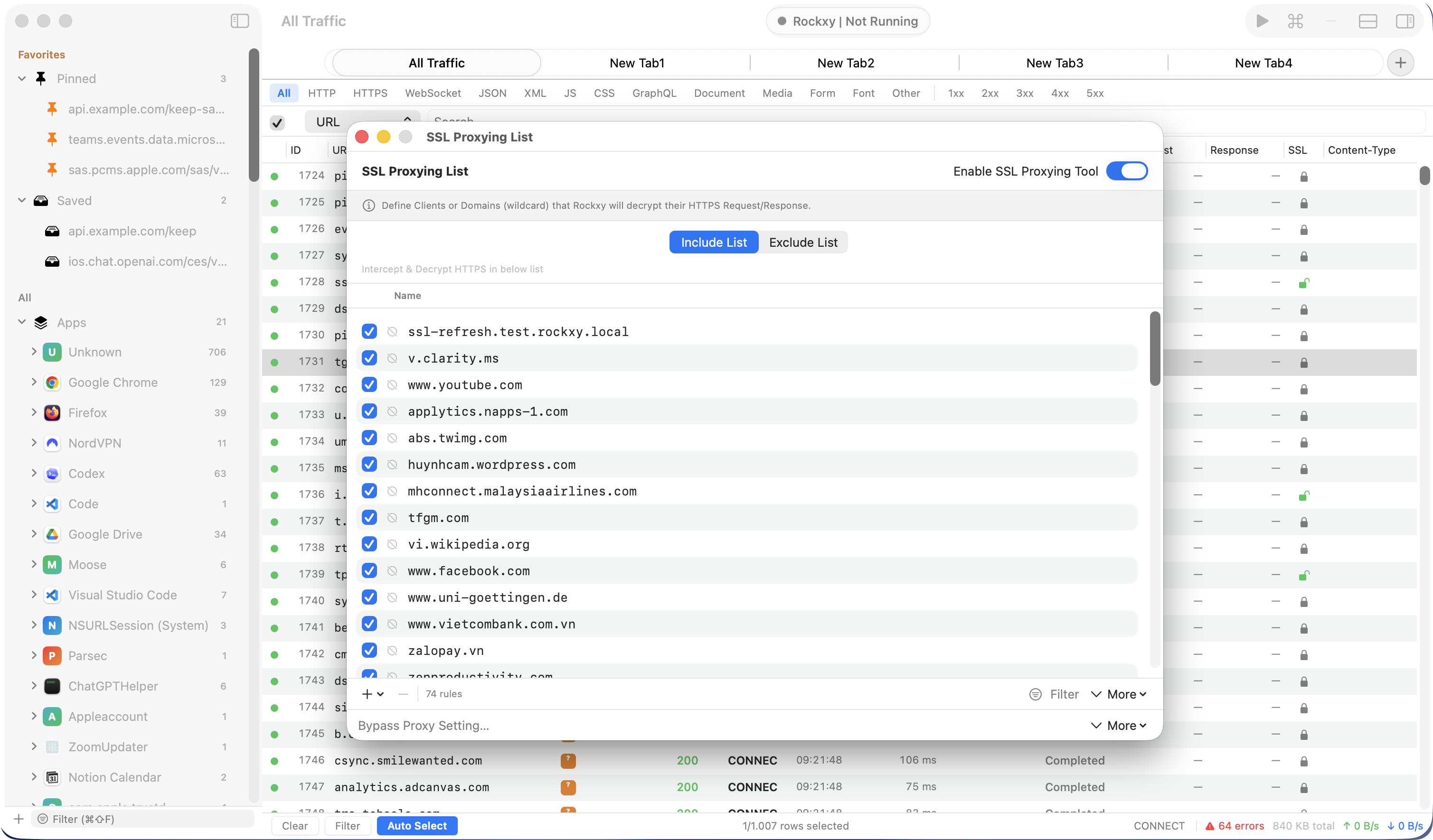
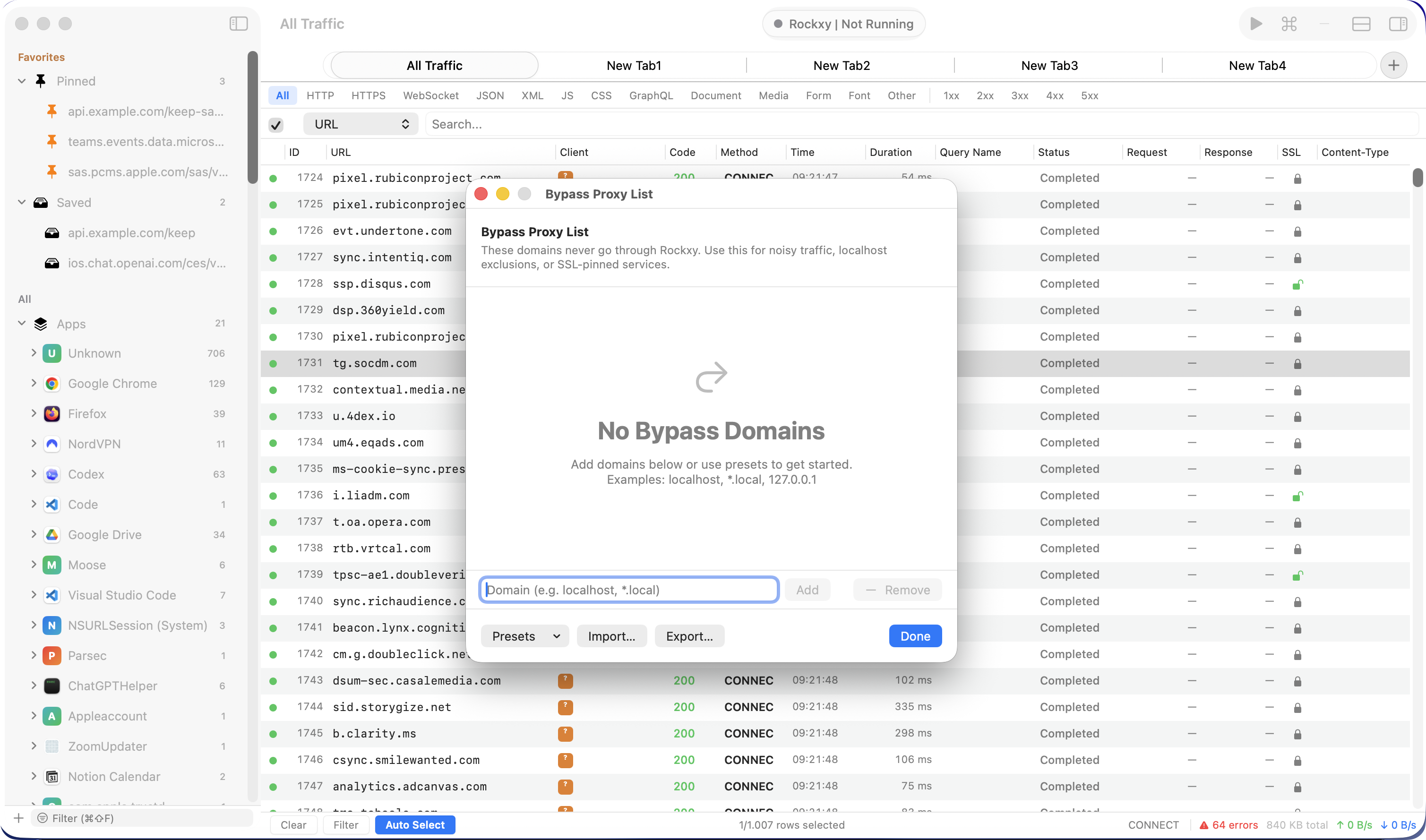
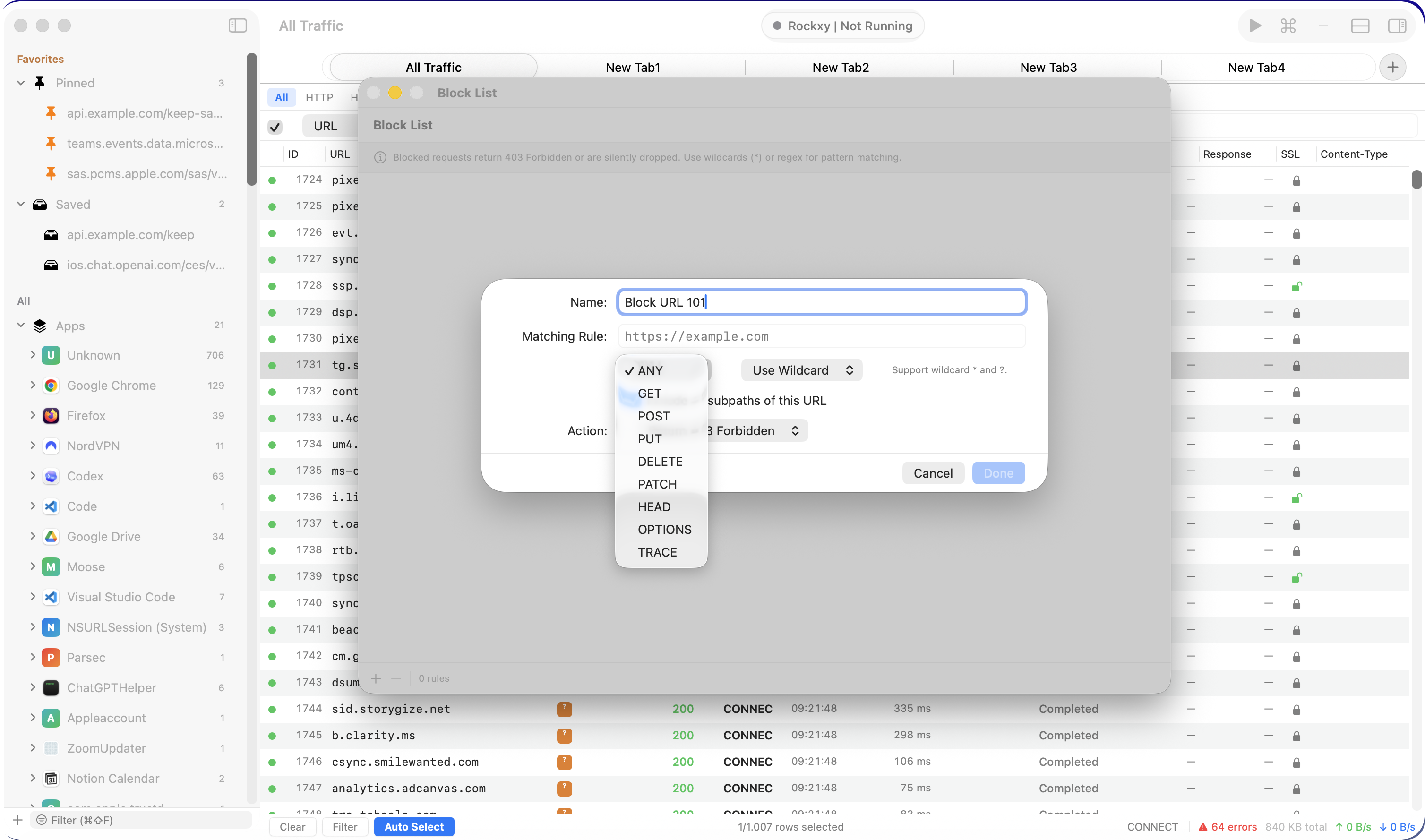
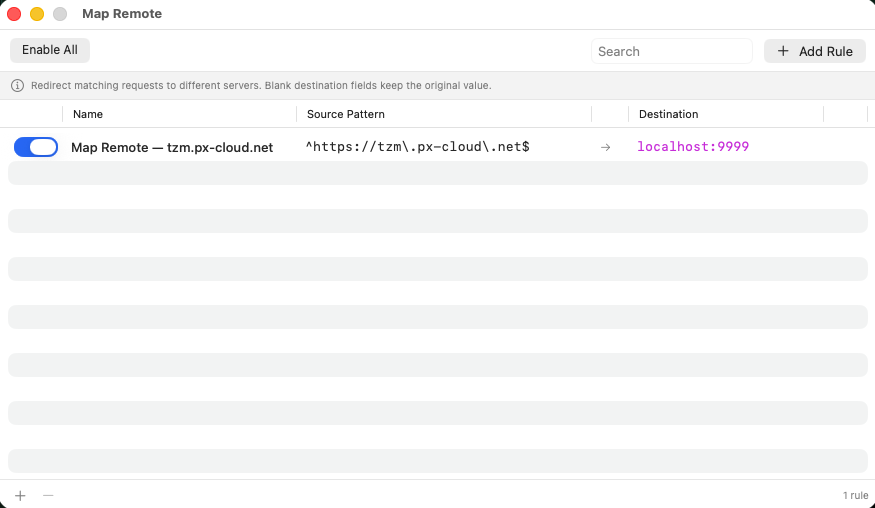
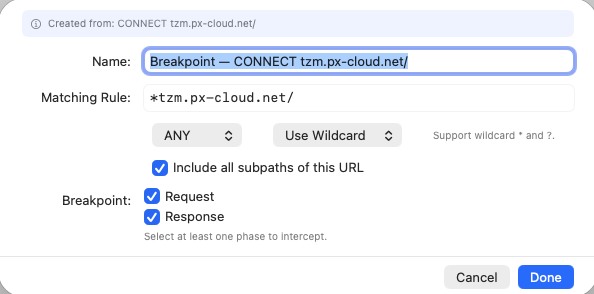
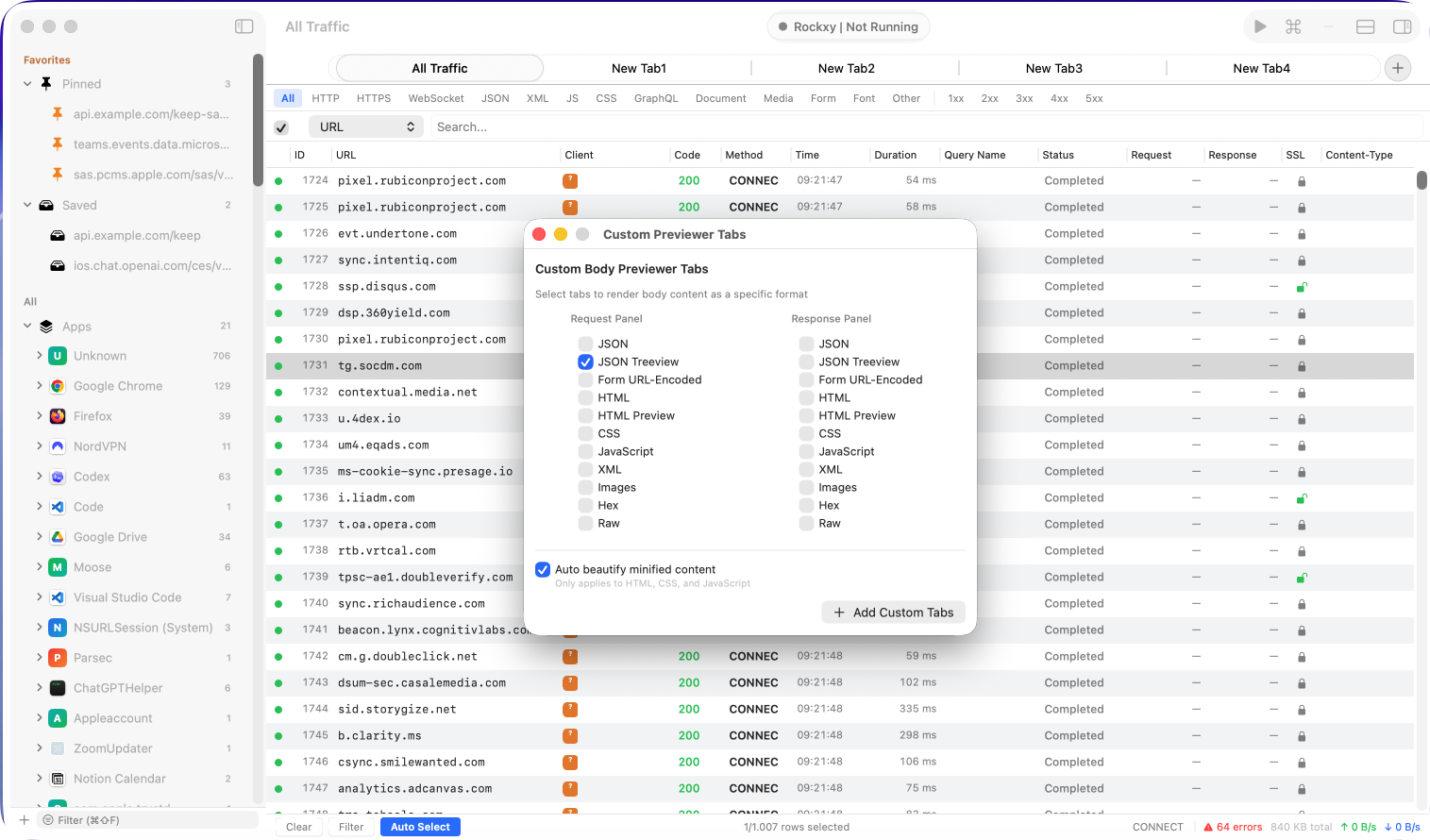
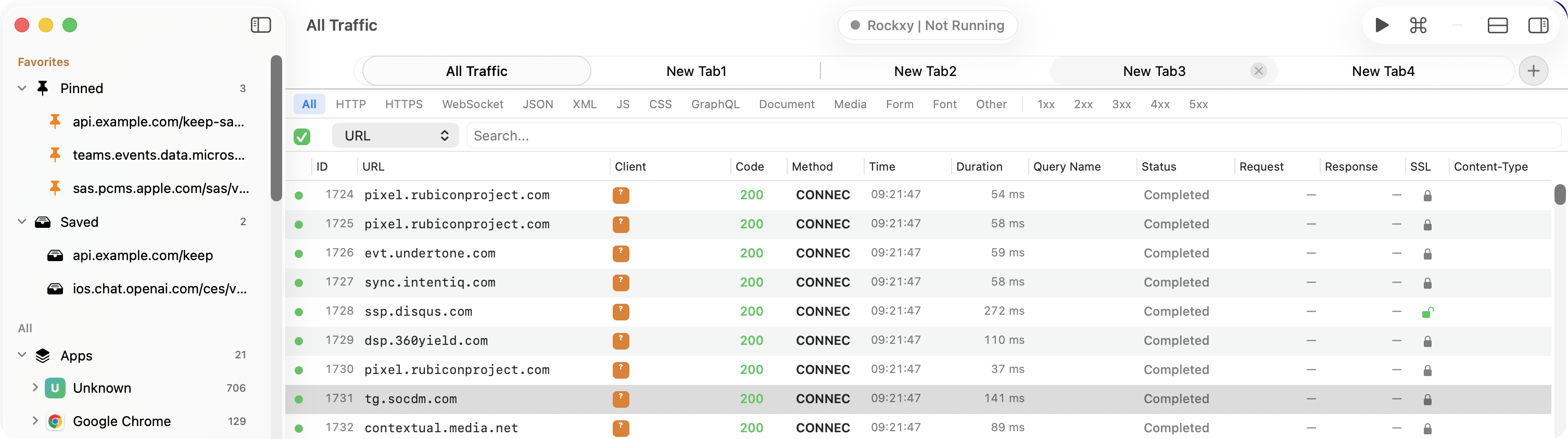
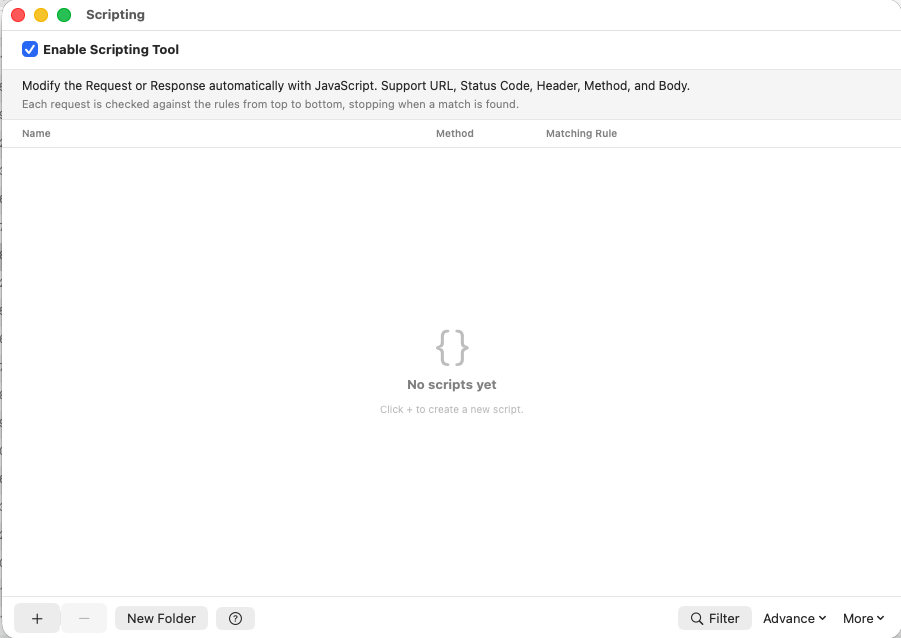
Rockxy is an open source proxy for Mac developers who need to see traffic from real apps, not just the browser. Use it to inspect API calls, pause and edit requests, replay failures, compare responses, export artifacts, and review the source before you trust the tool with sensitive traffic.
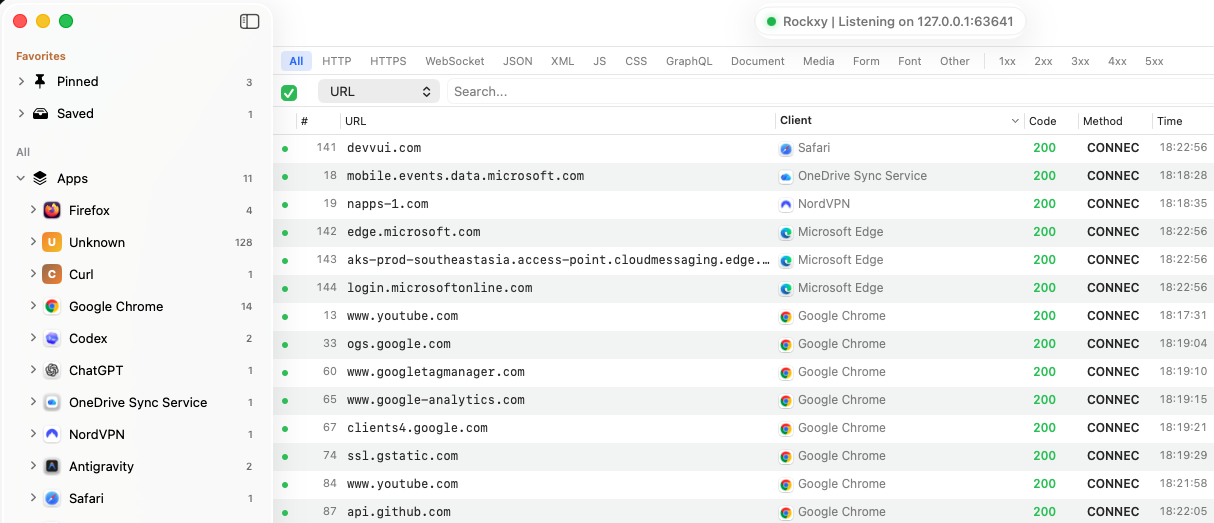
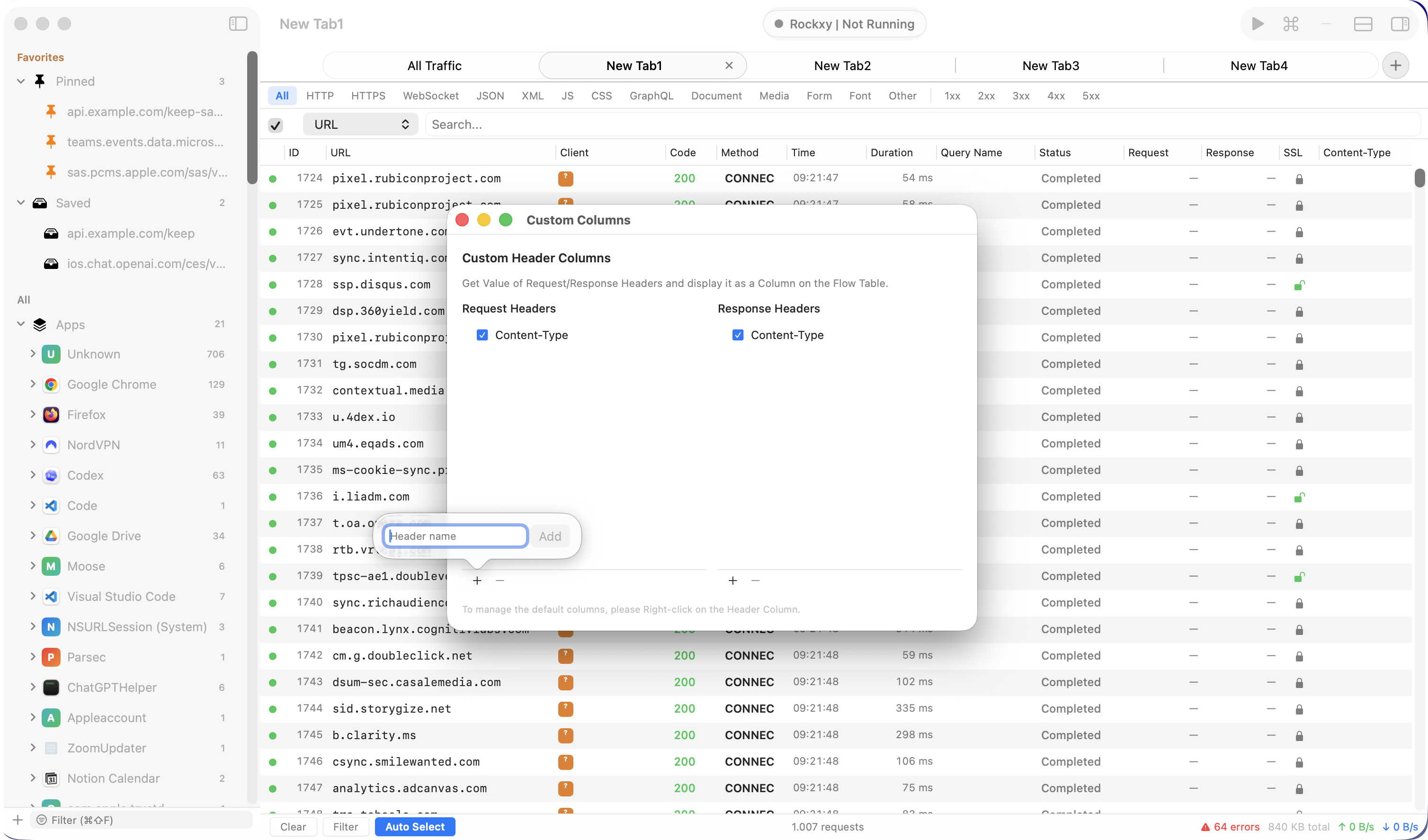
Traffic from real apps
HTTP, HTTPS, WebSocket, and GraphQL-over-HTTP traffic from native Mac apps, command-line tools, services, background processes, iOS devices, and iOS Simulator.
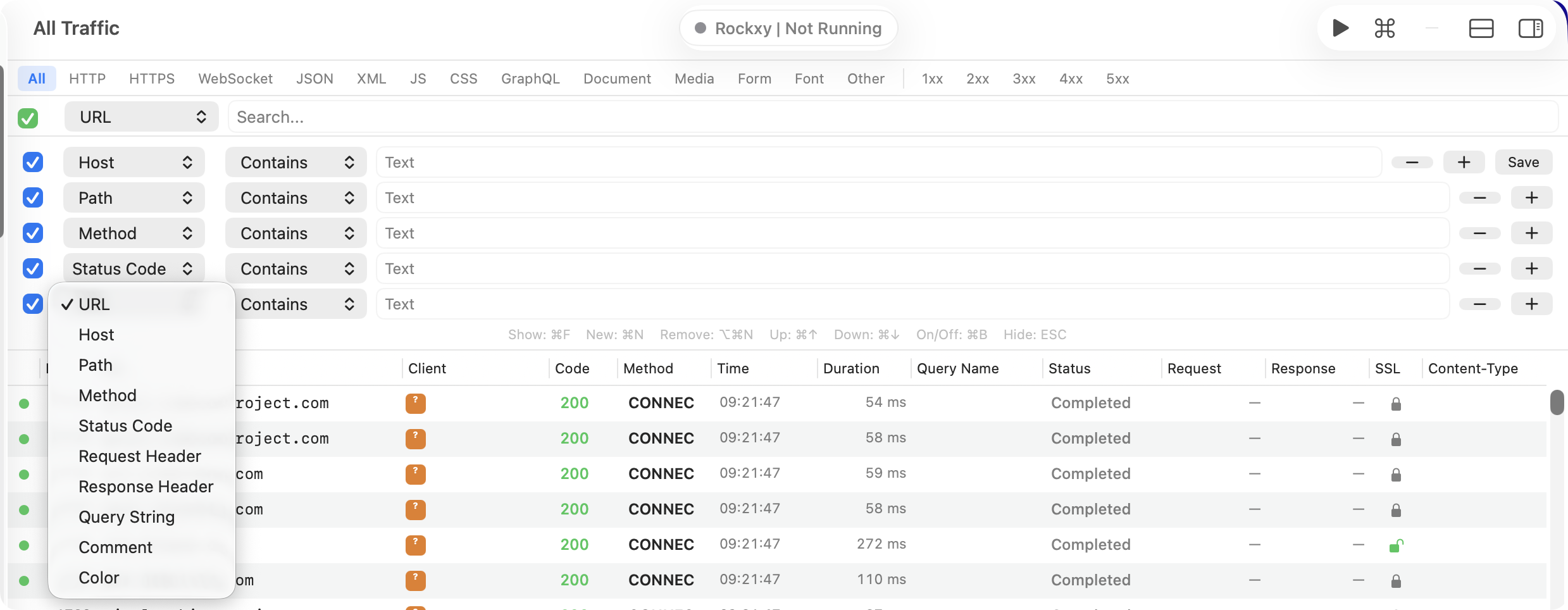
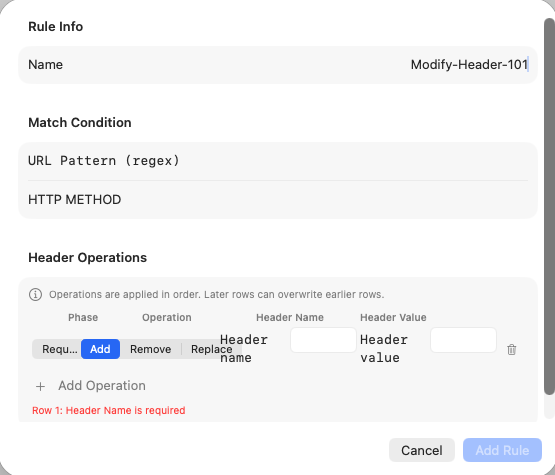
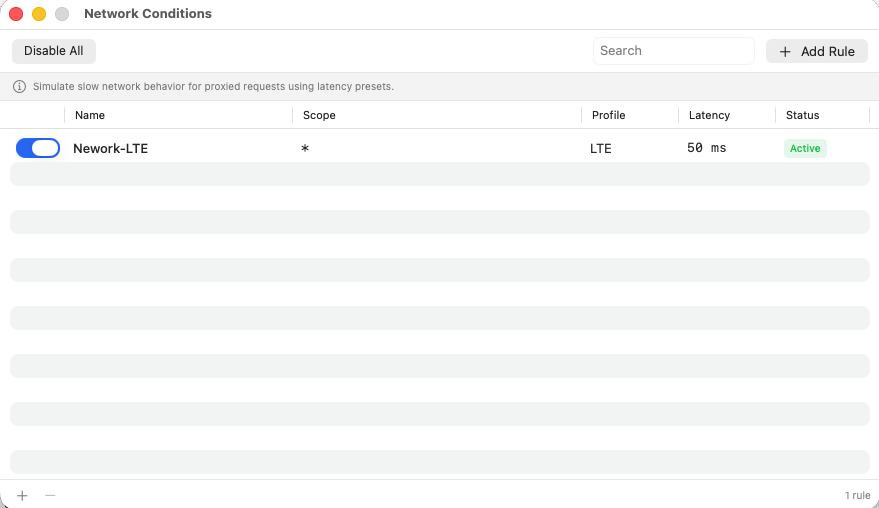
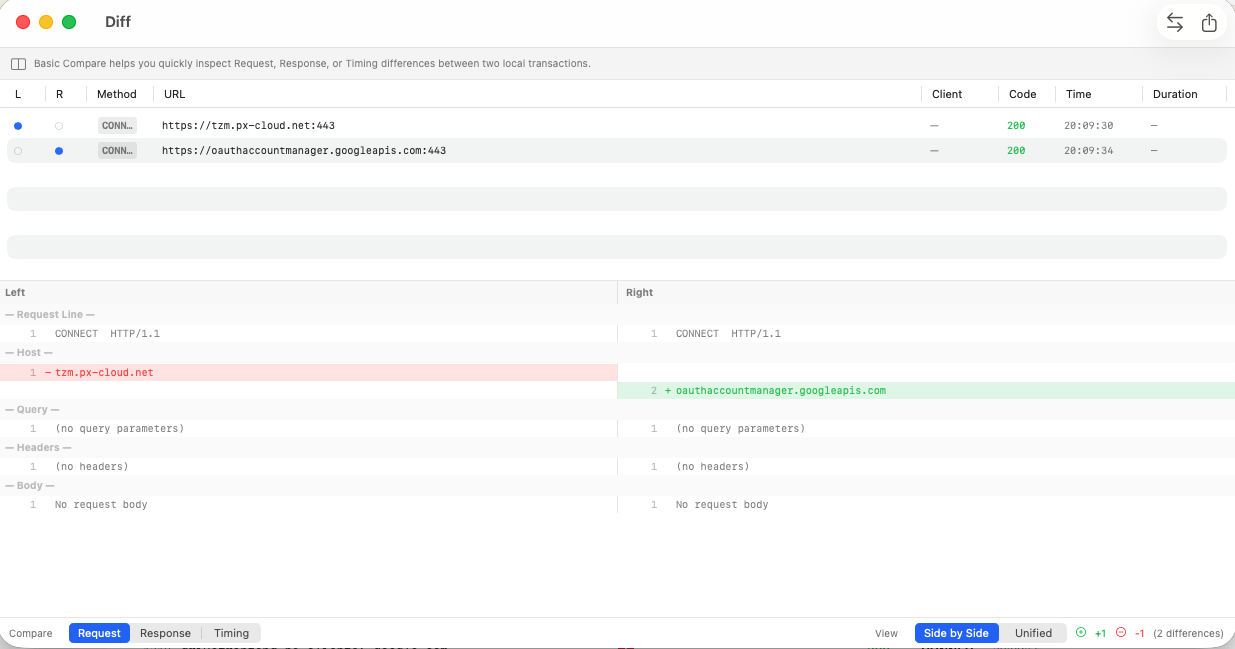
Debugging workflow
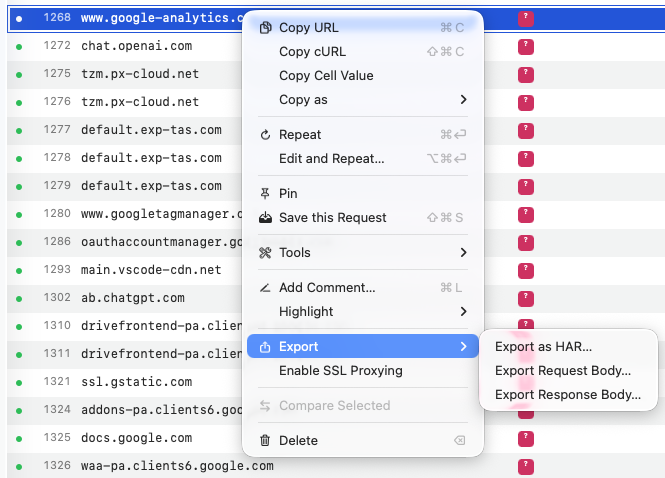
Inspect requests and responses, set breakpoints, rewrite traffic, replay requests, compare responses, export HAR, and save sessions for later analysis.
Public release trail
Signed universal macOS builds are published on GitHub Releases with versioned assets, release notes, and a SHA256 checksum.
Local-first evaluation
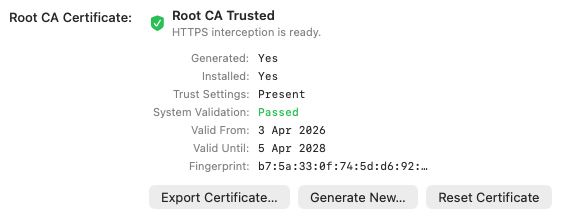
Check the source, issue tracker, release notes, privacy policy, and HTTPS interception docs before you install. Everything important is public.